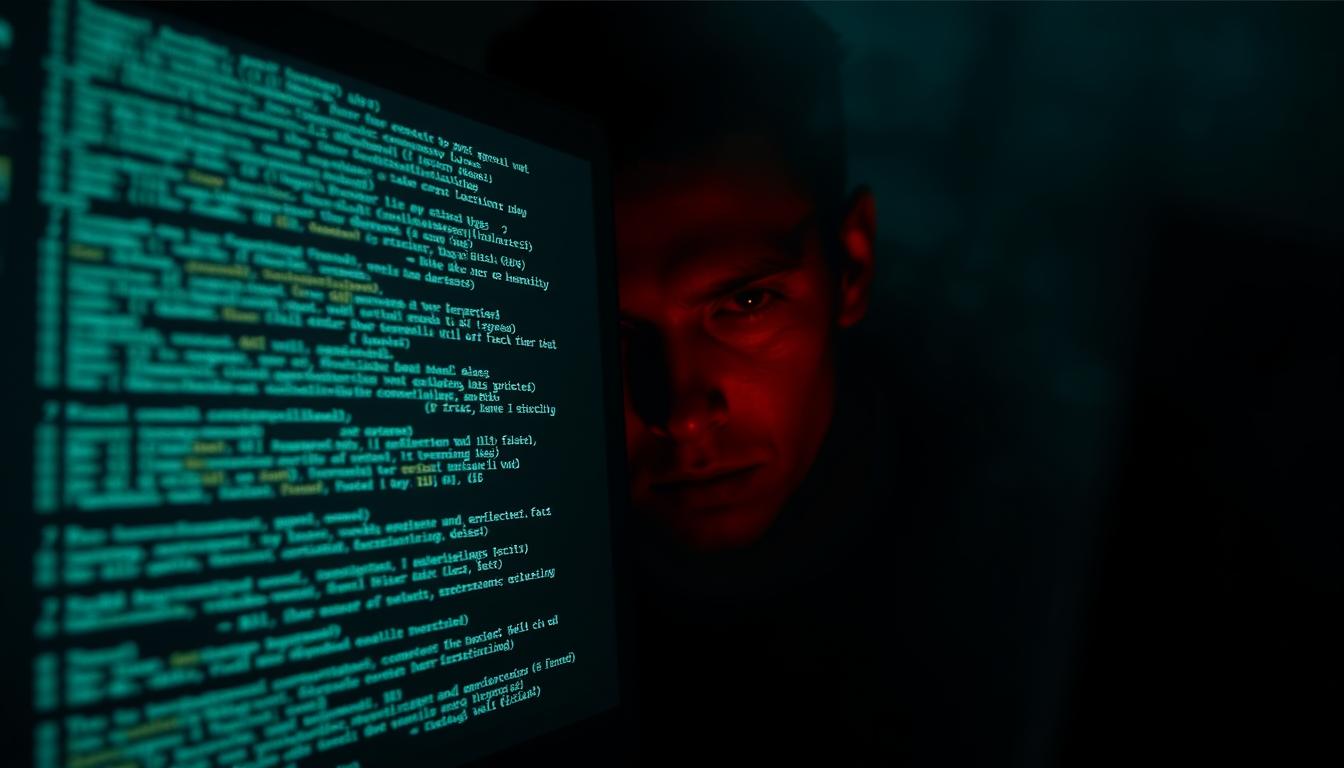
Cybercriminals Exploit CSS to Evade Spam Filters and Track Email Users’ Actions
Discover how cybercriminals leverage CSS Email Exploit techniques to bypass security measures, monitor user behavior, and conduct sophisticated phishing campaigns in email communications